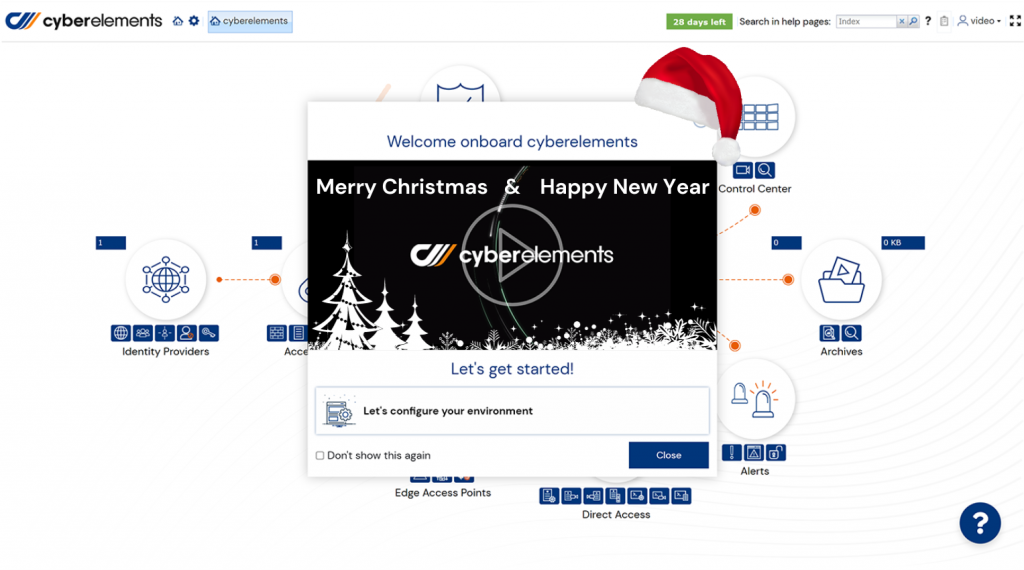
Set up your Zero Trust platform in 3 minutes!
Securely connect workforces to their applications & systems and ensure full control to the organization with a single platform for:
> Remote access (ZTNA) and privileged access (PAM)
> Secure access to IT & OT systems
> Workforce access and third party access
with cyberelements, secure all your business & privileged users and instantly give access to IT and OT systems.
Trusted by businesses of all shapes and sizes



Discover our customers challenges
See how we’ve helped thousands of organizations meeting their new security standards
![]()
![]()
![]()
It's up to you to test now!
Deploy your platform in less than 3 minutes
Deploy your Zero Trust platform in 3 minutes!
And learn how cyberelements can help your organization.
> Connect all users to apps and resources, anywhere
> Get full visibility on user behaviors and actions in real-time
> Restrict user access or actions based on user and device context
> Run on a full zero trust access policy
Discover in 40 sec. how to start your free trial
Try the cyberelements key features and many more
Session Monitorng & Real Time Analysis
cyberelements tracks in real time activities, detects and block any suspicious behaviour.
Organization & Personal Password Vault
Securely store all your credentials and keys. Define the right credentials to inject on the right session.

Identity-Based Access
Policies
Create policies to determine which applications & systems groups can access, and how.
Not sure yet?
Discover through these contents why it is time for you to deploy a Zero Trust SaaS platform that drives business performance
Vendor PAM: Why Is It Necessary to Deploy it?
Vendor Access Management Why is it necessary to deploy a vendor Privileged Access Management (vPAM) solution?
eBook: The 4 main Issues of Service Providers Access
Discover the 4 main issues of service provider access and how to respond to them efficiently thanks to PAM (Privileged Access Management).